Ledger warned that post-quantum cryptography designed to resist attacks from quantum computers could actually be vulnerable. hardware is not protected. This alert went viral on April 29, 2026 after demonstrating that the private key could be extracted without breaking the algorithm.
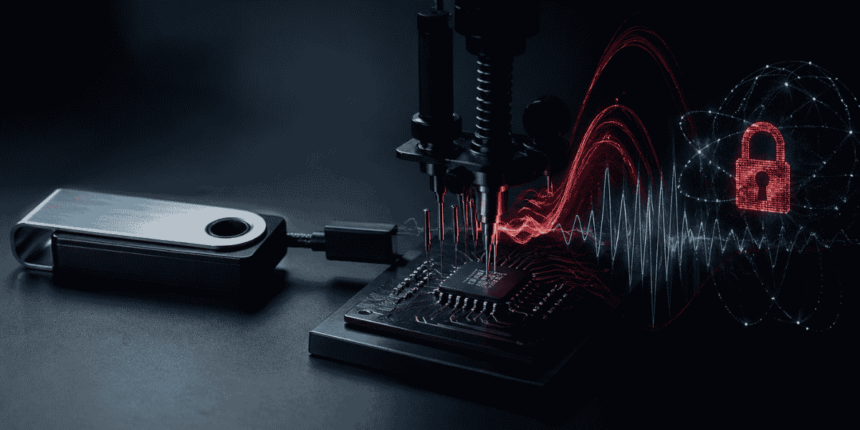
This risk is due to so-called side-channel attacks (side channel attackSCA), This is a method that is not about the mathematics of encryption, but about its execution. Instead of cracking the system, attackers observe indirect signals such as power consumption and electromagnetic emissions from the chip as it processes data. From these physical “leakages” it is possible to infer sensitive information such as private keys.
According to Ledger’s Donjon team, this type of attack is already possible in practical implementations of post-quantum cryptography. In tests run on a version open source ML-KEM algorithm (formerly known as Kyber), They were able to recover part of the private key using about 40 electromagnetic measurements. This process will complete within 1 minute.
As reported by CriptoNoticias, ML-KEM (Modular lattice-based key encapsulation mechanism) is a recently standardized algorithm within post-quantum cryptography. It is designed to secure key exchange even against quantum computers, based on a mathematical problem that is considered difficult to solve. but, Ledger’s experiments showed that theoretical strength does not prevent physical implementation from leaking information.
The impact is direct. devices like hardware walletSmart cards, IoT systems, and even mobile phones can be compromised if an attacker has physical access and the necessary equipment to measure these signals. In this scenario, security does not only depend on the algorithm, but also on how the algorithm is implemented. hardware.
To reduce this risk, Points out the need to incorporate specific measures for leisure. Among them, the most prominent one is masking (masking), splits the key into random parts. he shufflingchange the order of operations. The other is asynchronous, which results in variable execution times. These techniques aim to make correlation between the physical signal and the processed data difficult.
This caveat brings important nuance in the transition to post-quantum cryptography. It is not enough to have algorithms that are resistant to quantum computing. True security depends on running in an environment designed to avoid physical exposure. In practice, this means that users and businesses need to evaluate not only what cryptography to use, but also what types of devices and under what conditions the cryptography will be implemented.