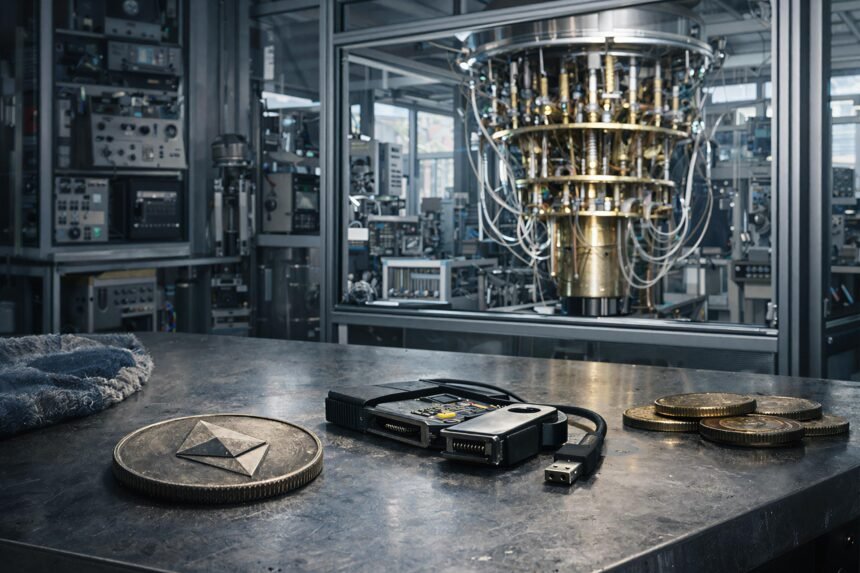
The crypto industry frames quantum computing as a single, catastrophic “Q-Day” moment when a sufficiently powerful machine arrives, shatters old cryptographic keys, and unravels the history of blockchains. This week, that moment may have been moved forward to this decade.
The Ethereum Foundation’s March 24 Post-Quantum (PQ) Roadmap indicates that the real quantum threat to Ethereum centers on forged signatures that enable theft and impersonation, and that the selection of stronger cryptographic algorithms is a relatively manageable layer of this problem.
The coordination infrastructure underneath is orders of magnitude more difficult.
The EF FAQ ranks published surfaces in a specific order. User accounts (externally owned accounts, or EOAs), exchange high-value operational keys, bridges, custody hot wallets, governance and upgrades multisig, and then validator keys.
Each category has a different migration schedule and political weight. Together, they describe a live financial system that has hundreds of millions of accounts and needs to upgrade itself while running at full capacity, with no acceptable flag days.
Account abstraction is the primary execution layer migration path for EF because it allows users to replace ECDSA-based authentication without forcing a reset of the entire chain.
The EIP-4337 infrastructure already supports over 26 million smart wallets and 170 million UserOperations, which is just a small portion of Ethereum’s active user surface.
DefiLlama is currently showing approximately 680,777 active Ethereum addresses, including 206,823 new addresses in the past 24 hours.
The Foundation’s timeline calls for an L1 protocol upgrade in approximately 2029, with full migration of the execution layer taking several more years. According to EF, most experts’ roadmaps place cryptography’s relevance in the early to mid-2030s.
The Global Risk Institute’s 2025 Quantum Threat Survey puts the probability of cryptographically relevant quantum computers appearing within 10 years at 28% to 49% and within 15 years at 51% to 70%, with respondents noting that that timeline is accelerating.
The overlap between L1 preparation and user wallet migration is where the operational risk really lies.
But that timeline looks set to get tighter this week. Google’s new warning will compress policy and market timelines, even if the scientific evidence remains uncertain. Google is currently planning for Q-Day in 2029. Although it is not certain when quantum computers related to cryptography will appear, the operational framework will change.
As major infrastructure operators start budgeting and planning for shorter time horizons, post-quantum readiness will cease to be a distant research topic and become a close-to-cycle execution problem for wallets, bridges, custodians, and validators.
Where capital and control are concentrated
Bridges and custody layers greatly increase that risk.
L2Beat shows that Ethereum-linked L2 has secured around $32.54 billion in value, while DefiLlama shows that Bridge protocols on Ethereum hold around $7.275 billion in total value locked, with BridgeRail processing around $18.835 billion in volume last month.
These flows pass through a relatively compact set of key management choke points, the very “high-value operational keys” that EF places second in its risk hierarchy.
TRM Labs’ January 2026 Crime Report found that infrastructure attacks against keys, wallets, and access control systems accounted for the majority of the $2.87 billion in cryptocurrency hacking losses in 2025, surpassing smart contract abuse.
The operational discipline required by the post-quantum roadmap in this space reflects the discipline that today’s industry is already failing, which is why the rotation of bridge and custody keys is urgently occurring on two timelines simultaneously.
The validator layer adds another dimension to the reconciliation problem.
Beaconcha.in shows approximately 976,204 active validators and 36.67 million ETH staked, which at first glance appears to be a maximally decentralized key migration problem.
At the entity level, Lido holds 21.24% of the net staking share, Binance 8.73%, Ether.fi 6.05%, and Coinbase 4.64%, giving these four operators a combined control of approximately 40.66%.
Validator key rotation is both a mass coordination problem and an operator focus problem.
| surface | Main status | why is it important | Type of risk | Migration challenges |
|---|---|---|---|---|
| User account/EOA | 680,777 active addresses. 206,823 new / 24 hours | largest live surface | Theft/Impersonation | Per-user migration |
| smart wallet rail | Over 26 million smart wallets. 170+ million user operations | Existing migration path | uneven recruitment | UX + wallet tools |
| bridge | TVL $7.275 billion. Monthly trading volume $18.835 billion | Value is concentrated in a small set of keys | Operational key compromise | Rapid organization rotation required |
| L2 linked to Ethereum | Secured a value of $32.54 billion | Large capital stacks rely on infrastructure | Indirect ecosystem spillover | Coordination between systems |
| validator | 976,204 people active. Staking 36.67 million ETH | Huge validator set | Network operation risks | Large-scale, intensive operator migration |
| Top staking entities | Lido 21.24%, Binance 8.73%, Ether.fi 6.05%, Coinbase 4.64% | Top 4 controls total 40.66% | Operator concentration | The leader sets the pace |
When major staking platforms rotate their keys early, migration momentum naturally builds and smaller validator cohorts follow a clear precedent. When large operators hold back, the burden of compliance falls disproportionately on independent validators, who lack the operational infrastructure to stand alone.
EF is assembling a dormant coin purse as the most political element of its roadmap.
Accounts that have never published their public keys will not be exposed to direct quantum exposure, as the keys will remain hidden within their addresses.
Accounts that make transactions, publish their public keys, and then go silent are an entirely different category, leaving their funds vulnerable with no self-migration mechanism.
EF’s FAQ lists two natural outcomes when the risk window arrives. Either do nothing or freeze vulnerable coins. EF explicitly frames its choices as community governance decisions, requiring social agreement about who will be protected and under what conditions.
EF estimates that Ethereum’s exposure in this category is around 0.1% of supply and Bitcoin’s exposure is closer to 5%, but this is related to an early address format that many believe has been abandoned.
Justin Saylor of a16z argued that Bitcoin is uniquely exposed because early P2PK outputs put public keys directly on-chain, and Bitcoin’s governance structure makes freezing arrangements politically stringent.
Glassnode shows that approximately 3.46 million BTC has been inactive for more than a decade, a widespread dormancy action that reveals why the debate over dormant coins is much more flammable for Bitcoin than for Ethereum.
2 results
Ethereum is based on an account abstraction infrastructure that is already running at scale.
If the EIP-7702 and EIP-4337 tools allow a large portion of active users to migrate before quantum anxiety reaches a retail tipping point, Ethereum can absorb the transition without triggering a governance crisis.
Bridges and custodians manage concentrated value, face organizational due diligence demands, move first, and establish industry-wide transition norms.
Due to Ethereum’s low dormancy exposure numbers, a policy of “doing nothing” remains politically viable and could avoid a contentious debate over freezing Ethereum.
The real advantage of Ethereum in that scenario is its upgrade agility. In other words, a live financial system that is quantum-ready through a phased, incentive-aligned transition that maintains continuity and user experience across the board.
However, if the L1 milestone declines, the execution layer transition will be deeper into the 2030s, and the highest value surface will remain partially anchored in traditional assumptions as the quantum timeline tightens. This is especially true if Google’s 2029 predictions come true.
As infrastructure attacks now account for most of the hacking losses, the market is starting to consider operational delays as a security discount for administrators and bridge operators before quantum computers become a reality.
Post-quantum readiness will become a standard due diligence standard for institutional investors, and businesses that cannot demonstrate a reliable transition schedule will face capital outflows and higher insurance costs.
Encryption threats are driven by market perceptions of operational delays that are much earlier than the encryption event, causing reputational and capital costs to accumulate during the transition window itself.
In February, EF placed its PQ work within the “Hardening L1” protocol track, explicitly linking native account abstraction to quantum readiness. Encryption proceeds on a predictable schedule.
Immigration battles over wallets, bridges, and dormant coins have already begun.
(Tag translation) Featured